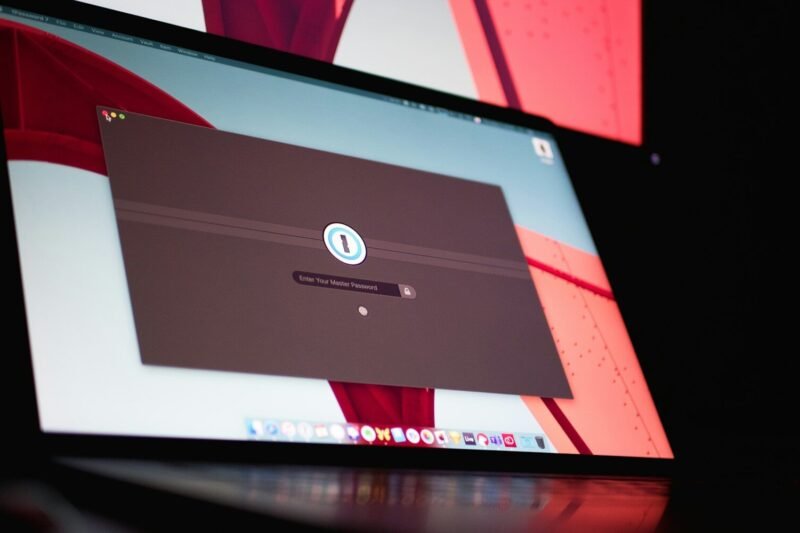
If you’ve ever wondered “are password managers safe,” this article explains the practical security advantages of using these tools, including how password managers generate strong, unique passwords, reduce risky habits like reusing passwords, and offer centralized, encrypted storage for your credentials—helping you protect your accounts more effectively against common cyber threats.
Author: theboss
How Password Managers Generate Secure Passwords
Learn how password managers generate secure passwords by using advanced algorithms and high-quality random number generators to create unique, complex passwords tailored to different website requirements, helping you protect your online accounts without the hassle of remembering multiple credentials.
Password Managers vs Browser Password Storage
Explore the key differences between password manager vs browser password storage, and discover how each option impacts your online security, convenience, and control over sensitive information—helping you make an informed decision for safer password management in your daily digital life.
Best Password Manager Features Explained
Discover the password manager features that go beyond simple storage—learn how encrypted vaults, convenient auto-fill tools, secure password generators, and in-depth security audits can strengthen your digital safety while streamlining your daily login process.
How Password Managers Protect Your Online Accounts
Discover how password managers protect your accounts by securely storing login details, generating unique passwords, and using advanced encryption to reduce risk from data breaches, so you can easily manage your online security with confidence.
What Is a Password Manager and Why You Need One
Discover what a password manager is and how it can transform your approach to online security—learn how these tools securely store and organize your passwords, generate strong credentials, and help protect your accounts from breaches, making it easier to maintain unique logins across all your devices.
Comprehensive Security Strategies for Managing Remote Administrative Access: Best Practices and Considerations
As organizations increasingly rely on remote administrative access to manage complex IT environments, the imperative for comprehensive security strategies becomes clear. Privileged access management for remote administrative security plays a pivotal role in mitigating the risks posed by dispersed endpoints, credential-based threats, and an expanded attack surface. Effective security frameworks must go beyond fundamental authentication to incorporate granular permissions, robust session monitoring, and continuous auditing, ensuring that only authorized personnel can execute sensitive operations while maintaining visibility and control across remote connections. By integrating best practices and rigorous controls, organizations can address both operational needs and the evolving threat landscape, safeguarding critical assets in an era of pervasive remote work.
A Comprehensive Guide to Detecting Insider Abuse of Remote Administration Tools
Effective insider threat detection for remote administration tools requires a nuanced approach that balances operational necessity with rigorous oversight. As organizations increasingly depend on Remote Administration Tools (RATs) for efficient IT support, the risk of insider abuse escalates—not only from malicious actors but also from negligent or compromised users. Recognizing the distinct patterns of insider exploitation, including unauthorized access, policy deviations, or unusual transfer activity, is essential. This comprehensive analysis examines the evolving landscape of insider threat detection as it pertains to remote administration tools, outlining proven monitoring strategies, alert mechanisms, and policy frameworks that mitigate risk without impeding legitimate IT workflows.
A Comprehensive Guide to Preventing Unauthorized Remote Access in Corporate Networks
As organizations navigate the ongoing evolution of distributed workforces and cloud integration, the integrity of enterprise remote access has emerged as a foundation of corporate security. Enterprise remote access security best practices are no longer optional guidelines but critical defenses against a rapidly expanding array of cyber risks. This guide delves into the complexities of remote connectivity, outlining both the technological and human dimensions that must be addressed to prevent unauthorized entry. Through in-depth analysis of threat vectors, access control mechanisms, and regulatory considerations, it equips enterprises with actionable strategies to protect sensitive assets, sustain operational continuity, and uphold trust in an increasingly interconnected business environment.
A Comprehensive Guide to Understanding Network Anomalies Caused by Remote Access Tools
Remote access tool anomaly detection has emerged as a critical component of modern network security, given the widespread use of both legitimate and malicious remote access tools (RATs) within contemporary IT environments. The complexities introduced by RATs manifest in the form of diverse network anomalies, ranging from subtle behavioral deviations to overt security incidents such as unauthorized access and data exfiltration. As organizations strive to maintain resilient infrastructures, the ability to discern between normal remote management activities and indicators of compromise remains paramount. Effective remote access tool anomaly detection therefore necessitates a detailed understanding of baseline network behaviors, the characteristics of authorized remote access, and the evolving tactics employed by adversaries who exploit similar technologies for nefarious purposes.