What is Back Orifice 2000 (BO2K)?
Safety notice: This site does not host BO2K installers, binaries, or “how-to” instructions.
The goal is historical context and defensive security awareness only.
Contents
- Short definition
- Historical background
- How it worked (high-level)
- Risks, classification, and dual use
- Defensive lessons today
- Primary sources and further reading
- FAQ
Short definition
Back Orifice 2000 (BO2K) was publicly presented in July 1999 as a networked Windows remote administration tool,
and it quickly became controversial because similar capabilities can also be used for unauthorized remote control.
In defensive security contexts, BO2K is commonly described as a backdoor / trojan risk when installed without
the knowledge and consent of the system owner.
Historical tagline: “Show Some Control”
— Cult of the Dead Cow (1999 release materials)
Historical background
In the late 1990s, Windows systems were widely administered with a mix of local tools, domain policies, and
third-party remote control products. BO2K entered public attention as part of a broader debate about Windows
security models, remote administration, and the risks of powerful tools being redistributed or repackaged for
unauthorized access.
Contemporary reporting described the release as widely anticipated and controversial, with arguments about whether
it was beneficial administration software or a tool that could lower the barrier to unauthorized entry.
How it worked (high-level)
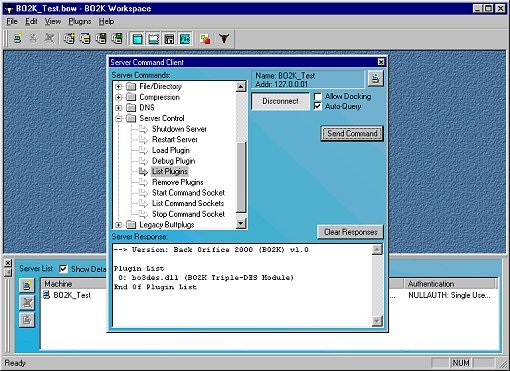
Historically, BO2K is most often described as a client/server-style remote administration suite with an extensible
plugin architecture. Contemporary sources emphasized that extensibility and optional cryptographic components could
change how the software behaved across builds and variants.
Client/server concept (non-operational)
At a conceptual level, remote administration tools separate a control interface (“client”) from a component
running on the managed machine (“server/agent”). That model can support legitimate administration when deployed
transparently and with consent, but it also creates obvious abuse potential if installed covertly.
Plugins and why defenders cared
A plugin architecture means features can be added or swapped without rewriting the entire program. In security
terms, this can complicate detection and incident response because variants may differ in network behavior and
capabilities. Defensive systems therefore tend to focus on observable signals (traffic patterns, suspicious
persistence, and policy violations) rather than relying on a single fixed signature.
What is intentionally not included here
The following is not published: configuration steps, operational commands, or instructions for deploying BO2K. This page is not a tutorial. It is historical context designed to support understanding and defense.
Risks, classification, and dual use
BO2K is frequently classified by security vendors as a backdoor trojan when used to obtain unauthorized remote
access. This classification focuses on how the software can be installed and used in practice, not on whether
remote administration as a concept can be legitimate.
Vendor framing (historical): “Back Orifice 2000 is a backdoor trojan program.”
— Symantec / SARC (1999)
Why “dual use” matters (and its limits)
Tools that can be used for system administration can also be repurposed for abuse. That reality is precisely why
modern security guidance places emphasis on consent, transparency, logging/auditing, least privilege, and trusted
software distribution channels.
Stealth mode controversy (historical context)
Contemporary debate focused on whether stealth features had legitimate administrative value or primarily served to
evade detection. That controversy is part of why BO2K became a durable reference point in discussions about
remote-control software, policy, and ethics.
Defensive lessons today
The lasting value of BO2K as a historical case study is not “how to use it,” but what it illustrates for defenders:
trust boundaries, software provenance, auditing expectations, and how rapidly “dual use”
tools can become abuse-enabling when redistributed outside controlled channels.
- Software trust: do not install untrusted software; treat remote-control tools as high risk.
- Policy and visibility: require consent, user notification where applicable, and audit trails.
- Network monitoring: focus on abnormal control traffic and unauthorized persistence signals.
Primary sources and further reading
I prioritize primary/official sources (publisher statements, Microsoft security guidance, and vendor advisories),
then university and major-media archives that document the release-era debate.
Primary / official
- cDc press release (1999-07-10)
- cDc joint statement (1999-07-19)
- Microsoft MS98-010 (Back Orifice context)
- Symantec/SARC definition (1999-07-13)
University and media archives
FAQ
Do you host BO2K downloads?
No. This page is prefered for historical documentation and defensive education only. BO2K binaries,
installers, “how-to” guides, or operational instructions are not provided.
Is BO2K “malware”?
In practice, BO2K has been widely treated as a backdoor/trojan risk when deployed without consent, which is why
many security vendors classified it accordingly. Remote administration as a concept can be legitimate; unauthorized
remote control is not.